Modern websites rely on cookies to manage the websites, deliver online services, and track users to deliver targeted ads.
The use of cookies is regulated by privacy laws such as Europe’s GDPR, Canada’s PIPEDA, Brazil’s LGPD, and others. There are different types of cookies. Most cookie types, such as targeting, advertising, or analytics, require obtaining cookie consent before dropping cookies on users’ devices.
Cookies that enable websites to function correctly are called strictly necessary cookies. Such cookies don’t require user consent, as they don’t collect any information about users.
Cookies are also classified as First-party cookies and Third-Party Cookies. When your website sets cookies on your customers’ browsers, such cookies are called First-party cookies. Third-Party Cookies are small scripts placed in a user's browser by a domain different from the one they are visiting. Third-Party Cookies are typically used for cross-site tracking to personalize ads and analyze user behavior across different websites.
Data privacy laws are much stricter on the use of Third-Party Cookies. Even some browsers block third-party cookies by default.
Besides cookies, there are also local storage and session storage, the use of which is also regulated by privacy laws. During a cookie audit you must also detect local storage and session storage.
If your business uses cookies to improve users’ experiences or deliver targeted ads, you need to conduct cookie audits to track how they’re used. Website owners need to know the types of cookies they are using, if they have third-party cookies, what cookie attributes are, and whether consent behavior is appropriate.
This guide will explain why you need a cookie audit, how to run a manual cookie audit in Chrome DevTools, and what to look for during cookie audits.
Why Manual Cookie Audits Still Matter in 2025?
So, what is a cookie audit?
A cookie audit is an inventory of all the cookies active on your website. The goal is to identify all the cookies on your site and their intended purposes, and ensure that they comply with applicable privacy regulations.
You need to know what cookies are running on your website. Even if you know what types of cookies are set, some cookies may be missing. For example, some website-building services install third-party cookies without your knowledge. To ensure compliance with GDPR, eprivacy Directive (EU cookie law), CCPA, and other digital privacy laws, you should know what type of cookies are present.
There are automated cookie scanners that can detect cookies on your website automatically. However, sometimes manual cookie audits are preferred, especially when your website has nuanced consent behavior or cookies that fire only under certain conditions.
A manual audit gives you context. You can see when cookies load, why they appear, and whether your consent banner controls them correctly.
To achieve full compliance with global and regional data privacy laws, you must perform cookie audits regularly.
Use CookieScript Cookie Scanner to automatically scan your website for cookies, local storage, and session storage, and add them to your site’s list of cookies:
What You Need Before Starting a Manual Cookie Audit
A manual audit doesn’t require much, but there are some recommendations that would help you perform it correctly.
Before starting a manual cookie audit, make sure you have:
- The website you’ll be testing
Production gives real results, staging is safer. - A clean browser session
It is advised to use an incognito mode. - Updated Chrome browser and access to Developer Tools.
- A basic idea of your site’s expected cookie behavior
You need this if some cookies load with a delay or when some conditions are met.
How to Run a Manual Cookie Audit in Chrome DevTools
To perform a manual cookie audit in Chrome DevTools, follow these steps.
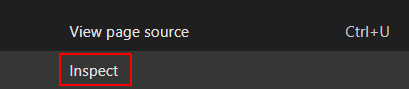
Step 1. Open Chrome DevTools
Open DevTools using one of these methods:
- Press F12,
- Press Ctrl + Shift + I (Windows) or Cmd + Option + I (Mac), or
- Right-click anywhere on the page and select Inspect.
Once it’s open, go to the Application tab. Depending on the size of your screen, you may need to expand your tab options at the top by clicking on the >> symbol:
![]()
Step 2. View cookies
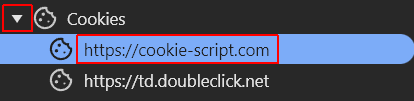
1. Under the Storage tab, select Cookies:

2. Select the website
When you click the triangle icon (left side of the Cookies tab), you will see all the available websites. Select the website you want to see cookies in Chrome:
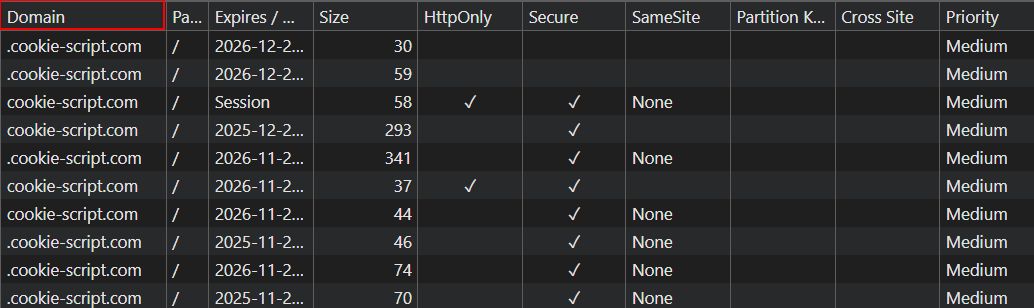
3. View cookies
Here you can see all cookies in Chrome. You can see different fields of cookies, whether Chrome cookies are secure, whether third-party cookies are running on the site, and other data about cookies.
Step 3. Categorize cookies
After you’ve analyzed your cookies, you need to categorize them based on the purposes they are used for.
There are the following cookie categories:
- Strictly necessary cookies: Cookies that are essential for a website to function properly, enabling core features like secure logins, user navigation, or shopping carts.
- Performance cookies: cookies that manage non-essential but beneficial tasks that help to increase the website’s performance.
- Functionality cookies: cookies that are used to remember user preferences and settings to enhance a website's performance and provide a more personalized experience.
- Advertising cookies: cookies that enable third-party ad providers to track data about users and deliver customized ads.
- Tracking cookies: cookies that monitor users online behavior and collect data like browsing history, preferences, and location for website analytics, user profiling, and personalized advertising.
Step 4. Document your cookie settings
Chrome doesn’t export cookies directly, but you can copy the table or take quick screenshots if that’s easier.
Step 5. Trigger your consent banner
You should test cookie behavior when users make their cookie choices. Press the Accept all, Reject all buttons on the Cookie Banner, or customize cookie settings if needed.
Step 6. View cookies repeatedly
Refresh the page and watch how cookies behave under each scenario (accept all, reject all, or customized cookie settings).
Note any cookies that load before consent or ignore user choices. You’re essentially testing the “before” and “after” states of cookies to see the changes.
It’s not enough to perform your privacy audit just once. Privacy laws evolve, and new legislations arrive. You should carry out an audit at least twice per year to ensure compliance.
Alongside regular audits, don’t forget to update your Cookie Policy when you introduce new cookies on your site.
Read also:
- How to check website cookies in Chrome and Firefox?
- How to view cookies in a web browser manually?
- How to view Google Analytics 4 cookies?
- All about cookies in the Chrome browser.
How to Understand Cookie Values
When you have a full list of all your cookies, you can analyze them. Look at each cookie and see what data it contains and how you collect, store, and use this data.
Analyze the following information about cookies:
- Name: The cookie's name.
- Value: The cookie's value.
- Domain: If the domain name corresponds with the website you are browsing, it means that these cookies are first-party cookies: If the domain name is different- these cookies are third-party cookies.
- Path: The URL that must exist in the requested URL in order to send the Cookie header.
- Expires / Max-Age: The cookie's expiration date or maximum age. This field shows which are session cookies and which are persistent cookies, that operate for a certain duration of time.
- Size: The cookie's size, in bytes.
- HttpOnly: If true, this means that it is a HTTP cookie. JavaScript modification is not allowed.
- Secure: If true, this means that the cookie is sent to the server only over a secure, HTTPS connection.
- SameSite: The SameSite cookie attribute is used by browsers to allow or block cookies based on attribute. It could contain Strict or Lax SameSite attributes.
- Partition Key: A cookie's partition key is the scheme and registrable domain of the top-level URL the browser was visiting at the start of the request to the endpoint that set the cookie.
- Priority: It is used with deprecated cookie priority attribute. Could contain Low, Medium (default), or High priority.
Watch different fields of cookies, export and document them. You can copy the table into spreadsheets or take quick screenshots for a quick view.
When you have a list of cookies before and after consent, and their properties, you can identify first-party vs third-party cookies, check cookie attributes, and detect high-risk or non-compliant cookies.
Here you can also edit or delete cookies. All the fields are editable except Size that updates automatically. Double-click a field to edit it.
How to Identify First-Party vs Third-Party Cookies
There are two types of cookies based on the domain of origin:
- First-party cookies come from the domain you’re currently visiting.
- Third-party cookies come from different domains that load scripts, embeds, ads, or tracking scripts from outside domains.
To identify first-party vs third-party cookies, open DevTools and look at the Domain column.
If cookies come from the domain you’re currently visiting, they are first-party cookies. Anything that doesn’t exactly match your domain is third-party.
For example, the figure below shows that a CookieScript blog article uses only first-party cookies:
You must obtain the user’s explicit consent for all third-party cookies. First-party cookies, if they are not strictly essential cookies, also require explicit consent.
With CookieScript, you can easily obtain GDPR compliant Cookie Consent. You can:
- Display a cookie consent banner on your website.
- Give users full control to accept, decline or change cookie settings on the banner.
- Customize the banner for desktop and mobile devices for accessibility.
- Show cookie table for full disclosure of cookies.
- Automatically block third-party cookiesthird-party cookies till the user gives consent.
- Record all user consents for proof of compliance.
How to Check Cookie Attributes (Secure, HttpOnly, SameSite, Expiration)
When you inspect cookies in Chrome DevTools, the attributes often tell you more about the cookie’s risk than its name or category.
You need to understand what different cookie attributes mean and what to look for during a manual cookie audit.
Secure attribute
A secure cookie attribute means that such a cookie can only be transmitted over HTTPS connections. This prevents the cookie from being sent over unencrypted HTTP, where hackers could catch it.
What to check during an audit:
- Any cookie handling personal data or session information must be Secure.
- If you see a cookie on an HTTPS site without the Secure flag, it usually means poor configuration or outdated code.
- Modern browsers expect Secure for almost everything except strictly necessary cookies.
HttpOnly attribute
HttpOnly cookies cannot be accessed by client-side JavaScript. This protects them from XSS attacks.
What to check during an audit:
- Sensitive cookies, such as session IDs or auth tokens, must always be HttpOnly.
- All important cookies (e.g., a login session) must be HttpOnly. If it’s not, that’s a red flag.
- Security-related cookies must always be HttpOnly. Analytics and functional cookies might omit this flag; however, it’s still recommended to mark them as HttpOnly.
SameSite attribute
The SameSite attribute controls whether cookies can be sent with cross-site requests. There are three possible values:
- Strict: Cookie stays within the same domain. Most private and secure.
- Lax: Allows some cross-site requests, but in a limited, safer way (e.g., top-level navigation).
- None: Cookie can be sent in all cross-site requests but must be Secure. It is used for third-party integrations.
What to check during an audit:
- First-party cookies generally should use Lax or Strict values.
- Cookies with SameSite=None are cross-site and often track users—check carefully their security and compliance.
- If SameSite=None is used without Secure value, that’s a compliance and security issue.
Expiration attribute
Expiration sets how long the cookie persists:
- Session cookies have no expiration date. They last only for a single browsing session and are deleted when the browser is closed.
- Persistent cookies include an expiration date and remain for days, months, or even years.
What to check during an audit:
- Persistent cookies must be justified under GDPR. You must have a clear, necessary purpose.
- Long lifetimes (e.g., 1–2 years) usually indicate tracking or profiling.
- strictly necessary cookies can be persistent cookies, but marketing cookies should not be long-lived without consent.
How to Detect High-Risk or Non-Compliant Cookies
A cookie becomes high-risk or non-compliant when:
- It loads before the user gives consent.
- It stores personal data or unique identifiers.
- It shares information with a third-party service.
- It lacks secure attributes (Secure, HttpOnly).
- It persists longer than necessary.
If you want to detect high-risk or non-compliant cookies, look for:
- Cookies that load before the user’s interaction with the Cookie Banner.
- Cookies with long lifetimes.
- Cookies that lack secure attributes (Secure, HttpOnly).
- Marketing or tracking labels.
- Cookies tied to analytics, ads, embedded widgets, and other third-party cookies.
If you’re unsure about the cookie, google the cookie name— it usually reveals its purpose and required attributes quickly.
How to Trace Cookie Behavior During Page Loads
You need the Network tab in Chrome DevOps tools for dynamic cookie tracing.
To trace cookie behavior during page loads, perform the following steps:
- Open the Network tab
Right-click anywhere on the page, select Inspect > Application > Network. Or press Ctrl + Shift + I, and go to the Network tab, or press F12 and go to the Network tab. - Refresh the page
Reload the page (through an icon or by pressing Ctrl + Shift + R) to see all network requests and responses, including the cookies they use. - Inspect requests
Click on a specific request to see its details. The Headers tab shows you the Set-Cookie header in the response (cookies being sent to the browser) and the Cookie header in the request (cookies being sent to the server). - Filter or search
Filter requests by the keyword cookie or by specific domain names.
This helps you detect cookies that load early, cookies tied to specific scripts, and cookies that fire right after certain actions.
You can also view cookies with JavaScript. To view cookies for the current domain, type document.cookie in the browser's console.
Testing Consent Behavior: Are Cookies Triggering Prematurely?
To perform a decent cookie audit, you should test consent behavior during all cookie choices made by a user, and check if cookies are triggering prematurely.
Test multiple scenarios:
- Do not interact with the Cookie Banner
Check which cookies appear before consent. - Reject all cookies
Press Reject all and then see if any marketing or analytics cookies still fire. - Accept all cookies
Press Accept all and compare against the scenario when you do not interact with the Cookie Banner. - Customize settings
See whether category-based consent is respected.
If a cookie appears when it shouldn’t, you’ve found a compliance issue.
Common Mistakes to Avoid During Manual Cookie Audits
When running manual cookie audits, businesses often face some issues, including:
- Not clearing cookies between tests
Non-session cookies remain after the session is closed. Clear cookies between tests; otherwise, you will see cookies from the previous session. - Not checking cookies triggered by user actions
When running manual cookie audits, you should also check cookies triggered by user actions, such as scrolling, clicking, or video playback. - Ignoring iframes or embedded content
Don’t ignore iframes or third-party services embedded on your site by partners. - Testing only one consent scenario
Test cookie firing after you press Accept all, Reject all, or accept some cookie categories. - Improper opt-outs
Merely logging a user's withdrawal isn't enough; the signal must be transmitted to all relevant third parties to stop data processing. - Using cached scripts without realizing it
To prevent cached scripts, open Chrome in incognito or manually clear cookies and scripts after each test. - Insecure logs
Storing audit logs in a format that is easily editable, like a simple spreadsheet, can compromise their validity. - Non-compliant banners
Test not only cookie behavior, but also the banner itself. Banners that block access to the site, use dark patterns, or make the reject option difficult to find or read, will not comply with data privacy laws.
When running manual cookie audits in Chrome, we recommend using incognito mode for each test run. This prevents from cached cookies, first-party scripts, or third-party scripts, that could remain from the previous sessions.
When to Use Automated Tools Instead of Manual Audits
Manual audits are great for precision, but they take time. Automated cookie scanners like CookieScript Cookie Scanner have the following advantages:
- Time saving
An automatic Cookie Scanner scans your website for cookies and analyzes them much faster than a manual cookie audit. - Accuracy
An automated cookie checker could detect cookies that may be missed manually. - Regular updates
You would perform manual cookie audit once or twice per year. Online cookie scanners check your website for new cookies regularly and update the report (once per month).
CookieScript Cookie Checker can scan your website and update the report much faster and easier for you.
Frequently Asked Questions
Why do you need to audit cookies?
Website cookies and other trackers collect Personal Information about website users. personal data collection and management are strictly regulated by data privacy laws such as GDPR, CCPA, or PIPEDA. To reach compliance with privacy laws, you need to perform an in-depth cookie audit to find all cookies your site uses, their purposes and types. You can perform a manual cookie audit using Chrome DevTools or with automatic cookie scanners like CookieScript.
Should I conduct a manual or an automatic cookie audit?
Manual audits provide greater control over each auditing stage. Automatic audits are quicker, simpler, more accurate, and are updated regularly. Unless you have a team with the right knowledge, an automatic cookie audit is usually recommended. You can use CookieScript Cookie Scanner for an automatic cookie audit.
How to identify first-party vs third-party cookies?
To identify first-party vs third-party cookies, open Chrome DevTools and look at the Domain column. If cookies come from the domain you’re currently visiting, they are first-party cookies. Anything that doesn’t exactly match your domain is third-party. You can also use automatic cookie scanner like CookieScript to detect and categorize cookies.
How to detect high-risk or non-compliant cookies during a cookie audit?
If you want to detect high-risk or non-compliant cookies, look for cookies that load before the user’s interaction with the cookie banner, cookies with long lifetimes, cookies that lack secure attributes (Secure, HttpOnly), marketing/ tracking labels, or cookies tied to analytics, ads, embedded widgets, and other third-party cookies.
How to trace cookie behavior during page loads?
You need the Network tab in Chrome DevOps tools for dynamic cookie tracing. Open the Network tab, refresh the page to see all network requests and responses, and inspect requests. The Headers tab will show you the Set-Cookie header in response (cookies being sent to the browser) and the Cookie header in the request (cookies being sent to the server).
How to test if cookies are triggering prematurely?
Performing a manual cookie audit with Chrome DevOps tools, test multiple scenarios: do not interact with the cookie banner, reject all cookies, accept all cookies, or customize settings, and see whether cookie choices or category-based consent are respected. If a cookie appears when it shouldn’t, you’ve found a compliance issue.